【愚公系列】2023年08月 攻防世界-MOBILE(人民的名义-抓捕赵德汉1-200)
【摘要】 前言下面介绍两个反编译工具jadx是一个用于反编译Android APK文件的开源工具,静态反编译,查找索引功能强大jeb和IDA很像,属于动态调试,可以看java汇编也可以生成伪代码,还可以动态attach到目标调试对于so文件的逆向工具选择IDA逆向工具是一款反汇编器,被广泛应用于软件逆向工程领域,能够反汇编各种不同平台的二进制程序代码,并还原成可读的汇编代码。 一、人民的名义-抓捕赵...
前言
下面介绍两个反编译工具
- jadx是一个用于反编译Android APK文件的开源工具,静态反编译,查找索引功能强大
- jeb和IDA很像,属于动态调试,可以看java汇编也可以生成伪代码,还可以动态attach到目标调试
对于so文件的逆向工具选择
- IDA逆向工具是一款反汇编器,被广泛应用于软件逆向工程领域,能够反汇编各种不同平台的二进制程序代码,并还原成可读的汇编代码。
一、人民的名义-抓捕赵德汉1-200
1.题目
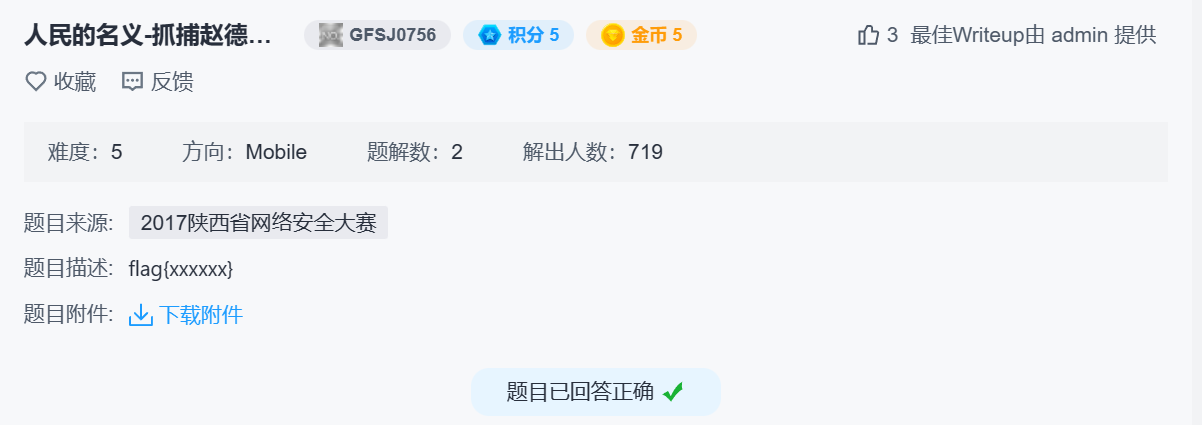
2.答题
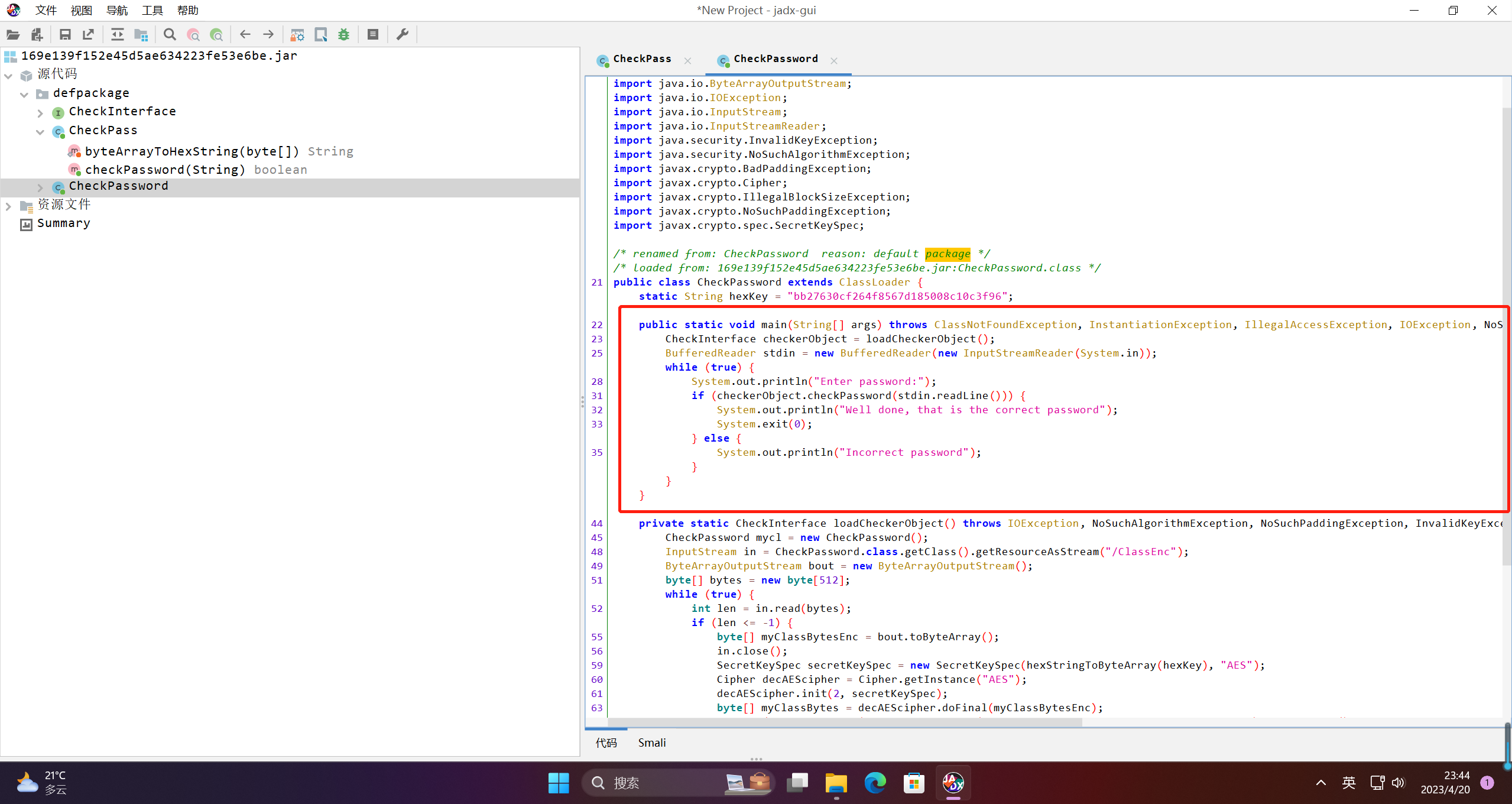
简单看一下三个类文件,可以发现,checkPassword类基础自ClassLoader,并实现了main方法。也就是这个jar文件的入口函数。
package defpackage;
import java.io.BufferedReader;
import java.io.ByteArrayOutputStream;
import java.io.IOException;
import java.io.InputStream;
import java.io.InputStreamReader;
import java.security.InvalidKeyException;
import java.security.NoSuchAlgorithmException;
import javax.crypto.BadPaddingException;
import javax.crypto.Cipher;
import javax.crypto.IllegalBlockSizeException;
import javax.crypto.NoSuchPaddingException;
import javax.crypto.spec.SecretKeySpec;
/* renamed from: CheckPassword reason: default package */
/* loaded from: 169e139f152e45d5ae634223fe53e6be.jar:CheckPassword.class */
public class CheckPassword extends ClassLoader {
static String hexKey = "bb27630cf264f8567d185008c10c3f96";
public static void main(String[] args) throws ClassNotFoundException, InstantiationException, IllegalAccessException, IOException, NoSuchAlgorithmException, NoSuchPaddingException, InvalidKeyException, IllegalBlockSizeException, BadPaddingException {
CheckInterface checkerObject = loadCheckerObject();
BufferedReader stdin = new BufferedReader(new InputStreamReader(System.in));
while (true) {
System.out.println("Enter password:");
if (checkerObject.checkPassword(stdin.readLine())) {
System.out.println("Well done, that is the correct password");
System.exit(0);
} else {
System.out.println("Incorrect password");
}
}
}
private static CheckInterface loadCheckerObject() throws IOException, NoSuchAlgorithmException, NoSuchPaddingException, InvalidKeyException, IllegalBlockSizeException, BadPaddingException, ClassFormatError, InstantiationException, IllegalAccessException {
CheckPassword mycl = new CheckPassword();
InputStream in = CheckPassword.class.getClass().getResourceAsStream("/ClassEnc");
ByteArrayOutputStream bout = new ByteArrayOutputStream();
byte[] bytes = new byte[512];
while (true) {
int len = in.read(bytes);
if (len <= -1) {
byte[] myClassBytesEnc = bout.toByteArray();
in.close();
SecretKeySpec secretKeySpec = new SecretKeySpec(hexStringToByteArray(hexKey), "AES");
Cipher decAEScipher = Cipher.getInstance("AES");
decAEScipher.init(2, secretKeySpec);
byte[] myClassBytes = decAEScipher.doFinal(myClassBytesEnc);
return (CheckInterface) mycl.defineClass(null, myClassBytes, 0, myClassBytes.length).newInstance();
}
bout.write(bytes, 0, len);
}
}
private static byte[] hexStringToByteArray(String s) {
int len = s.length();
byte[] data = new byte[len / 2];
for (int i = 0; i < len; i += 2) {
data[i / 2] = (byte) ((Character.digit(s.charAt(i), 16) << 4) + Character.digit(s.charAt(i + 1), 16));
}
return data;
}
}
CheckPassword包含用户密码输入的判断
package defpackage;
import java.security.MessageDigest;
import java.security.NoSuchAlgorithmException;
/* renamed from: CheckPass reason: default package */
/* loaded from: 169e139f152e45d5ae634223fe53e6be.jar:newClassName.class */
public class CheckPass implements CheckInterface {
@Override // defpackage.CheckInterface
public boolean checkPassword(String input) {
MessageDigest md5Obj = null;
try {
md5Obj = MessageDigest.getInstance("MD5");
} catch (NoSuchAlgorithmException e) {
System.out.println("Hash Algorithm not supported");
System.exit(-1);
}
byte[] bArr = new byte[40];
md5Obj.update(input.getBytes(), 0, input.length());
return byteArrayToHexString(md5Obj.digest()).equals("fa3733c647dca53a66cf8df953c2d539");
}
private static String byteArrayToHexString(byte[] data) {
StringBuffer buf = new StringBuffer();
for (int i = 0; i < data.length; i++) {
int halfbyte = (data[i] >>> 4) & 15;
int two_halfs = 0;
do {
if (halfbyte < 0 || halfbyte > 9) {
buf.append((char) (97 + (halfbyte - 10)));
} else {
buf.append((char) (48 + halfbyte));
}
halfbyte = data[i] & 15;
two_halfs++;
} while (two_halfs < 1);
}
return buf.toString();
}
}
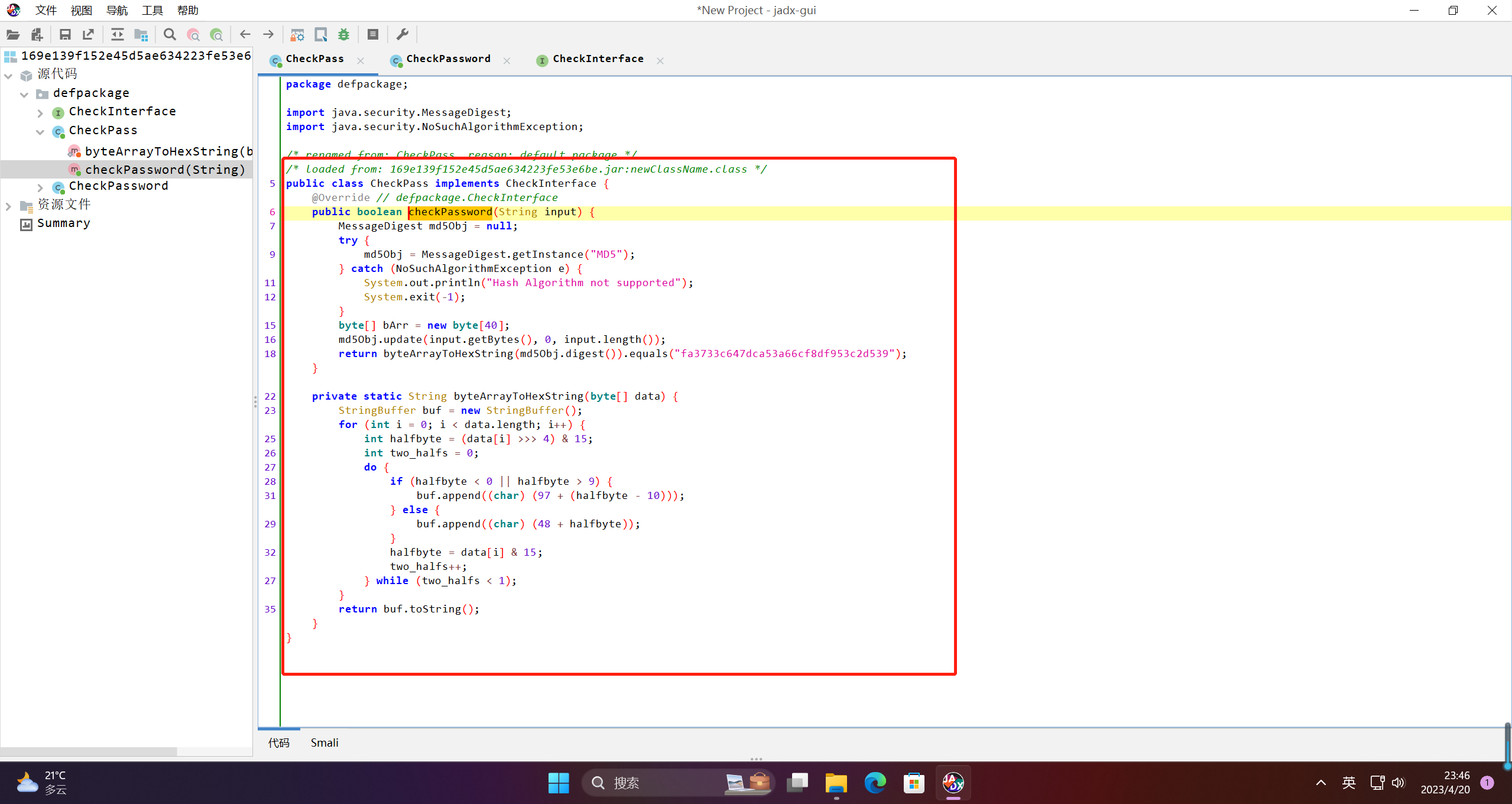
可以看到用户输入就是:fa3733c647dca53a66cf8df953c2d539的md5解密
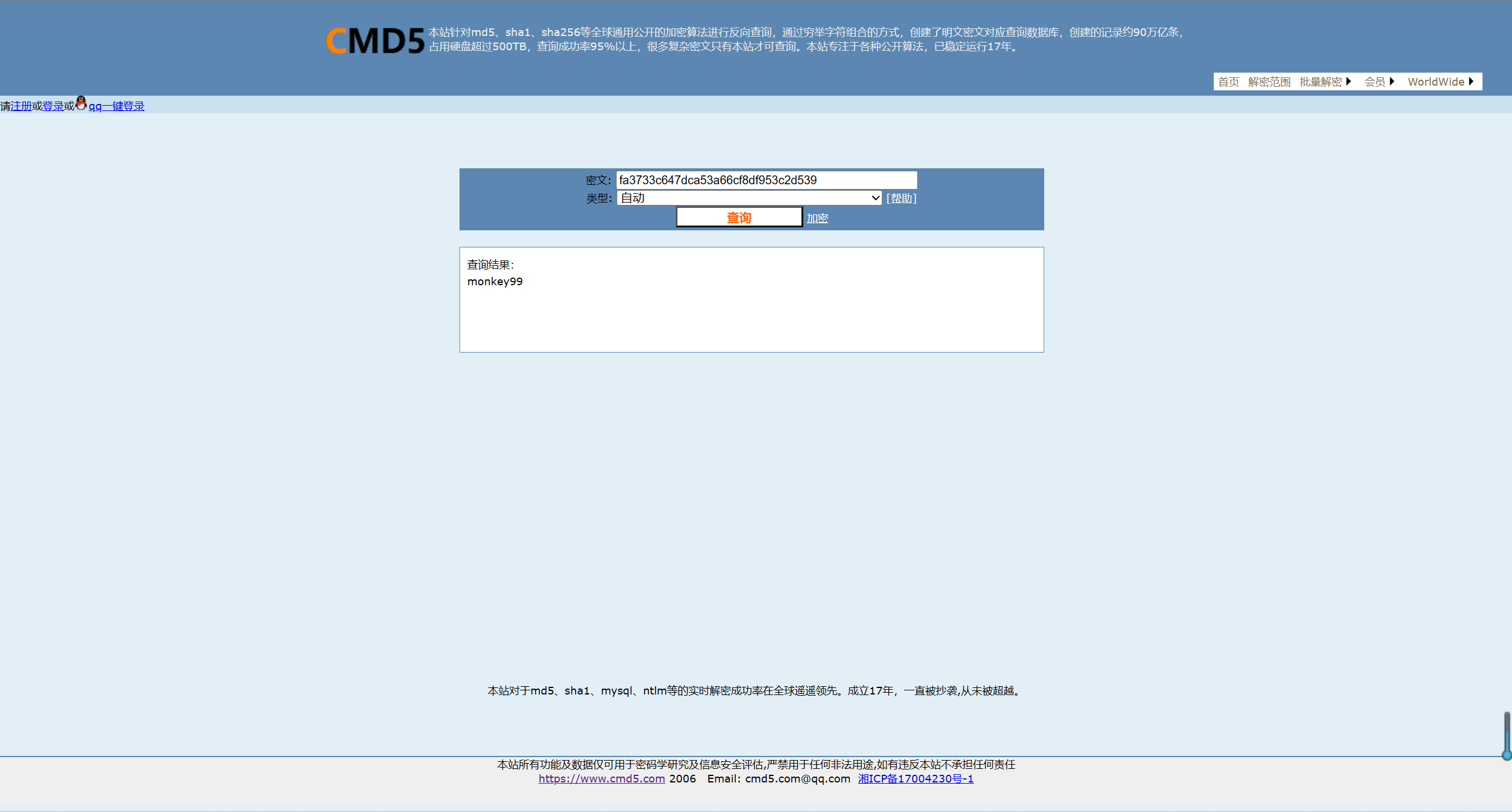
得到flag:flag{monkey99}
【声明】本内容来自华为云开发者社区博主,不代表华为云及华为云开发者社区的观点和立场。转载时必须标注文章的来源(华为云社区)、文章链接、文章作者等基本信息,否则作者和本社区有权追究责任。如果您发现本社区中有涉嫌抄袭的内容,欢迎发送邮件进行举报,并提供相关证据,一经查实,本社区将立刻删除涉嫌侵权内容,举报邮箱:
cloudbbs@huaweicloud.com
- 点赞
- 收藏
- 关注作者


评论(0)